Trendmicro has been able to identify a new point-of-sale (PoS) malware family that has affected more than 100 victim organizations in Brazil. We have dubbed this new malware family as “FighterPOS”. (This name is derived from BRFighter, the tool used by the author to create this new threat.) This one-man operation has been able to steal more than 22,000 unique credit card numbers.
Its creator appears to have had a long history in carding, payment scams, and malware creation; in addition we believe that this malware author acted independently and without any accomplices or associates. FighterPOS is not cheap. It is currently priced at 18 bitcoins (currently worth around US$5,250). However, its control panel is well-designed and it supports a wide variety of features that may be useful to attackers.
This blog post outlines the behavior of FighterPOS, with more technical details available in our paper entitled FighterPOS: The Anatomy and Operation of a New POS Malware Campaign.
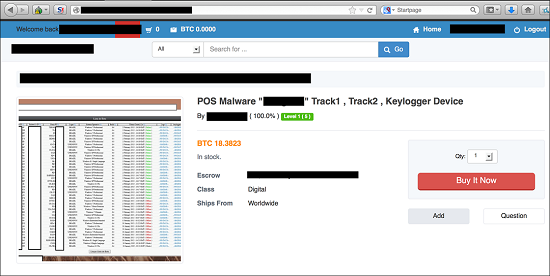
Purchasing
At first glance, the advertisement is not particularly unusual. What piqued our interest was the professional nature of the ad and the malware’s supported features.
Figure 1. Advertisement selling FighterPOS
The control panel and malware is currently being sold for 18.3823 BTCs, or roughly US$5,250. While this may seem expensive, the opportunity to make that money back is relatively easy. The buyer could potentially resell each credit card received right away, or use it at a later time. If the buyer wants an additional executable and panel instance, the author charges an additional US$800.
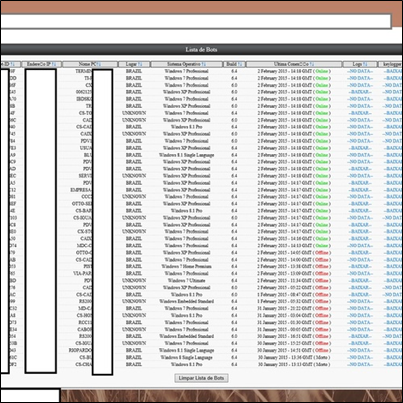
Figure 2. FighterPOS Control Panel
The author, who went by the username cardexpertdev, clearly stated in the ad that the executable is not fully undetectable (FUD), stating that the individual will need to use a crypting service to ensure the malware is undetectable by antivirus scanners. This is common when PoS malware is created, and crypting services are traditionally required to bypass many defensive security controls.
FighterPOS was not the only product related to credit card fraud that cardexpertdev was selling. He was also selling credit card numbers, EMV chip recorders, and other similar fraud-related products and tools to other cybercriminals.
Victimology
Data obtained from the C&C servers indicate that FighterPOS has infected approximately 113 PoS terminals, more than 90% of which were found in Brazil. Evidence of system infection in other countries, including the United States, Mexico, Italy, and the United Kingdom was also found.
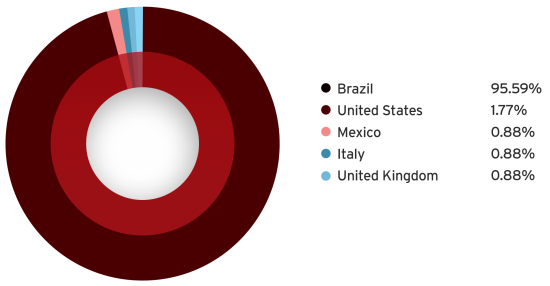
Figure 3. Distribution of FighterPOS-affected machines
Together, the infected systems have sent 22,112 unique credit card dumps for a single month (late February to early April) to the FighterPOS operator. Many of the victims of FighterPOS are users of Linx MicroVix or Linx POS systems – both popular software suites in Brazil.
FighterPOS Functionality
The functionality of FighterPOS is similar to other PoS malware families we’ve seen in the past. It is capable of collecting credit card track 1, track 2, and CVV codes. The malware also contains a RAM scraping functionality, commonly seen in many PoS malware families. Additionally, its keylogger functionality allows the attacker to log all keystrokes on the infected terminal. The code for the RAM scraping functionality is similar to that found in NewPosThings.
Two malware samples that gained our attention were IE.exe (MD5 hash: 55fb03ce9b698d30d946018455ca2809, detected as TSPY_POSFIGHT.SM) and IEx.exe (MD5 hash: 55fb03ce9b698d30d946018455ca2809), which both connect to the C&C server located at hxxp://ctclubedeluta.org/.
Both of the samples are written in Visual Basic 6. Although Visual Basic 6 is considered outdated and antiquated, applications written in this language still work, even on fully patched systems.
One may ask why a “new” PoS malware family is built on such an old platform as Visual Basic. We believe that this is because FighterPOS code is not entirely new. Instead, the vnLoader malware (designed for botnets) was modified to add PoS-specific features. It retains its botnet-oriented capabilities, which include:
-
Malware auto-update
-
File download and execution
-
Sending out credit card data
-
Sending out keylogged data
-
Layer 7 or layer 4 DDoS attacks
The DDoS capability effectively turns this POS family into a very flexible and attractive tool for prospective buyers.
Conclusion
FighterPOS is a full-featured piece of malware, carefully developed using strong encryption. It supports multiple ways to talk with its C&C infrastructure. Its keylogging capabilities allow for DDoS attacks and gaining full control of victim machines. We currently estimate that each infected machine sends back ten new credit card numbers to the attackers.
We are continually evaluating this threat, and are still performing research not only on the malware family, but also the C&C infrastructure.
Indicators of Compromise
The SHA1 hashes of the FighterPOS samples we’ve seen are as follows:
-
361b6fe6f602a771956e6a075d3c3b78 – TSPY_POSFIGHT.SM
-
55fb03ce9b698d30d946018455ca2809 – TSPY_POSFIGHT.SM
-
af15827d802c01d1e972325277f87f0d – TSPY_POSFIGHT.SM
-
b99cab211df20e6045564b857c594b71 – TSPY_POSFIGHT.SM
-
e647b892e3af16db24110d0e61a394c8 – TSPY_POSFIGHT.SM
We have seen the following C&C servers and sites in use:
-
69.195.77.74
-
ctclubedeluta.org
-
msr2006.biz
-
sitefmonitor.com
via: trendmicro




Leave a Reply