In these times of unabated data breaches, the typical Chief Information Security Officer (CISO) must feel like a moving target in a shooting gallery. It’s not a matter of whether an attack and possible breach will occur, it’s a matter of when. Being a CISO is a fascinating and important job. Often, though, it’s a thankless one.
Unfortunately for CISOs, their role is one of the positions held most accountable when a data breach occurs. According to one survey, 21 percent of IT decision-makers would most likely blame a data breach on the CISO, ranking second only behind the CEO.
CISOs can – and should – take steps well in advance to mitigate the possibility of their company falling victim to a data breach. And should a breach occur, this will help them hang on to their position.
In this article, we explore some of the ways that CISOs can avoid being perceived as a mere scapegoat and suggest how they can contribute in a more meaningful way to the company’s IT security posture and even enhance the organization’s brand.
What is a CISO?
Since the CISO role has only been in existence for a decade or two, some people aren’t even sure what the CISO does. This may contribute to the casting of blame after a data breach. In short, the CISO (chief information security officer) is the senior-level executive who’s responsible for executing and overseeing the company’s cybersecurity strategy.
CISO responsibilities may include:
- Hiring IT security staff
- Conducting employee security awareness training
- Developing secure business policies and practices
- Planning for disaster recovery
- Monitoring the IT environment for vulnerabilities and abnormal events
- Ensuring the privacy and security of customer data
- Identifying the most important security metrics and KPIs
- Evaluating and purchasing security products from vendors
- Managing responses to cybersecurity incidents
- Verifying the company’s compliance with laws and regulations
With IT environments becoming increasingly more complex and vulnerable by the day, the responsibilities of the CISO have expanded over time. Handling all of these obligations appears to be an impossible and somewhat underappreciated task. According to one estimate, the average tenure of a CISO is 18 months. Although it’s prestigious and well-paid, the CISO role is a high-stress one where firings and resignations are more common than in other executive positions.
How Can CISOs Protect the Company and Themselves?
ACCURATE AND REGULAR REPORTING
If a security flaw is found in an organization’s IT infrastructure, but that information is shielded from the public, will the CISO be fired? Operational transparency is key. That means comprehensive, accurate, and consistent reporting of vulnerabilities, any non-compliant infrastructure, and data security incidents — no matter how minor they may seem. As a best practice, this open approach can aid in the prevention as well as detection, identification, and investigation of the inevitable data breach when it occurs.
In one particularly egregious case, a CISO promised thousands of dollars to a penetration tester who discovered a vulnerability in the company’s server but then failed to report the problem to the CEO. The CISO also did not pay the tester and continued to ignore the tester’s attempts at contact. Fortunately, the CEO fired the CISO immediately once he discovered this negligence in failing to share the information and pay the person responsible for finding the vulnerability.
HIRING THE RIGHT TEAM
CISOs should focus on hiring the right security professionals for the job whatever their background may be. The “skills gap” in tech is even more pronounced in IT security, and many security professionals are self-taught. At IBM, 20 percent of U.S. cybersecurity hires in the past three years are so-called “new-collar” positions, which emphasize aptitude, skills, and competence over degrees and previous careers.
This shift in hiring means that CISOs can prioritize on-the-job employee training and focus on finding the optimal aptitude and best cultural fit rather than the “right” degree. CISOs can use tests during the hiring process in order to assess candidates’ decision-making skills, ability to learn, and aptitude for handling security issues.
MAKING SURE THE BOARD HEARS THEIR VOICE
In recent years, the CISO has reached a level of strategic importance in many organizations that is equal to the CIO (chief information officer). This means that the CISO fully deserves a place at the table in the executive boardroom.
One common trend for company hierarchies is to have the CISO report directly to the CEO, which helps improve their working relationship. Although CISOs can do little to control the company’s reporting structure, it’s important that their voice is heard by the executive team since so much of an organization’s business continuity and brand reputation rests upon successful data security strategy and execution.
USING THE RIGHT SOLUTIONS AND TOOLS
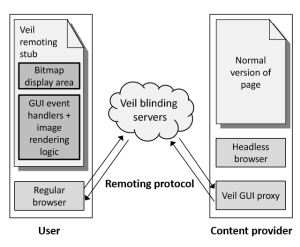
Legacy data security architectures that utilize firewalls and IDS/IPS have become insufficient at providing the protection that’s required to ensure the safety and privacy of the data environment.
Forrester notes in a recent data security report that “perimeter-based approaches to security have become outdated. Security and privacy pros must take a data-centric approach to make certain that security travels with the data itself—not only to protect it from cybercriminals but also to ensure that privacy policies remain in effect.”
Due to the highly valuable sensitive data that they possess, financial services organizations are particularly susceptible to insider threats. Implementing an encryption solution provides true data-centric protection and guards against unauthorized access to data stores, helping to reduce and prevent data exfiltration by insiders and outsiders alike. This supports the Center for Internet Security’s (CIS) data protection recommendation. The CISO must also give careful consideration to who has access to any and all encryption keys, reinforcing CIS’s controlled use of administrative privileges.
Other solutions that the CISO must be responsible for choosing are vulnerability assessment software and monitoring solutions.
EMPLOYEE EDUCATION AND TRAINING
One of the primary responsibilities of CISOs is making employees more aware of security issues like malware and phishing and helping them to adopt best practices. Knowing about cyberattack techniques and preventative actions is meaningless unless the CISO works to share that information with the rest of the organization.
CONTAINING THREATS IMMEDIATELY
Even with all the right precautions in place, cyberattacks can still happen as hackers become more aggressive and sophisticated. CISOs who can reduce or eliminate dwell time by identifying and containing the threat as soon as possible will minimize the disruption and damage to the business, succeeding where other CISOs have failed. Investing in advanced security tools and technologies like data-centric audit and protection, which leverages analytics and machine learning, can reap massive dividends for both CISOs and their organizations.
Final Thoughts
CISOs are an incredibly important resource, but all too often they find themselves the scapegoat in the event of a data breach. However, there are steps that CISOs can take to protect themselves and their company:
- Building the right team
- Establishing ongoing education and training programs
- Choosing the right tools and solutions
- Providing consistent reporting
- Staying in close communication with leadership
CISOs who proactively perform these activities will not only improve their organizations’ security posture; they will decrease the likelihood of finding themselves out of a job when the inevitable occurs.
via: tripwire