Next time when you see an advertisement of your favorite pair of shoes on any website, even if it is legitimate, just DO NOT CLICK ON IT.
…Because that advertising could infect you in such a way that not just your system, but every device connected to your network would get affected.
A few days ago, we reported about a new exploit kit, dubbed Stegano, that hides malicious code in the pixels of banner advertisements rotating on several high profile news websites.
Now, researchers have discovered that attackers are targeting online users with an exploit kit called DNSChanger that is being distributed via advertisements that hide malicious code in image data.
Remember DNSChanger? Yes, the same malware that infected millions of computers across the world in 2012.
DNSChanger works by changing DNS server entries in infected computers to point to malicious servers under the control of the attackers, rather than the DNS servers provided by any ISP or organization.
So, whenever a user of an infected system looked up a website on the Internet (say, facebook.com), the malicious DNS server tells you to go to, say, a phishing site. Attackers could also inject ads, redirect search results, or attempt to install drive-by downloads.
The most worrisome part is that hackers have combined both threats in their recent widespread malvertising campaign, where DNSChanger malware is being spread using Stegno technique, and once it hit your system, instead of infecting your PC, it takes control of your unsecured routers.
Researchers at Proofpoint have discovered this unique DNSChanger exploit kit on more than 166 router models. The kit is unique because the malware in it does not target browsers, rather it targets routers that run unpatched firmware or are secured with weak admin passwords.
Here’s How the Attack Works:
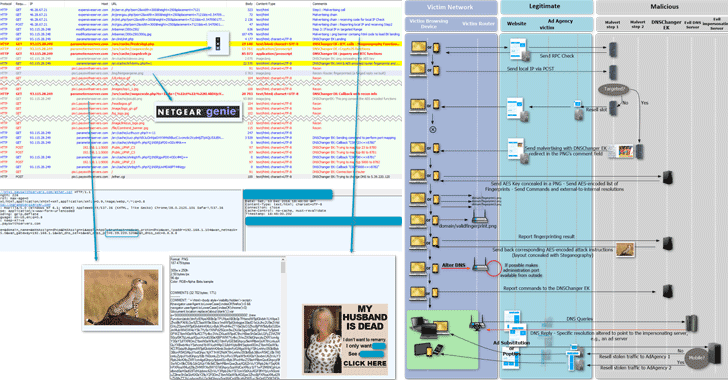
Firstly, the ads on mainstream websites hiding malicious code in image data redirects victims to web pages hosting the DNSChanger exploit kit. The exploit kit then targets unsecured routers.
Once the router is compromised, the DNSChanger malware configures itself to use an attacker-controlled DNS server, causing most computers and devices on the network to visit malicious servers, rather than those corresponding to their official domain.
Those ads containing malicious JavaScript code reveals a user’s local IP address by triggering a WebRTC request (the web communication protocol) to a Mozilla STUN (Session Traversal Utilities for NAT) server.
STUN server then send a ping back containing the IP address and port of the client. If the target’s IP address is within a targeted range, the target receives a fake ad hiding exploit code in the metadata of a PNG image.
The malicious code eventually redirects the visitor to a web page hosting DNSChanger, which uses the Chrome browser for Windows and Android to serve a second image concealed with the router exploit code.
“This attack is determined by the particular router model that is detected during the reconnaissance phase,” a Proofpoint researcher wrote in a blog post. “If there is no known exploit, the attack will attempt to use default credentials.”
List of Routers Affected
The attack then cloaks traffic and compares the accessed router against 166 fingerprints used to determine if a target is using vulnerable router model. According to researchers, some of the vulnerable routers include:
- D-Link DSL-2740R
- NetGear WNDR3400v3 (and likely other models in this series)
- Netgear R6200
- COMTREND ADSL Router CT-5367 C01_R12
- Pirelli ADSL2/2+ Wireless Router P.DGA4001N
It is not clear at the moment that how many people have been exposed to the malicious ads or how long the campaign has been running, but Proofpoint said the attackers behind the campaign have previously been responsible for infecting more than 1 million people a day.
Proofpoint did not disclose the name of any ad network or website displaying the malicious advertisements.
Users are advised to ensure that their routers are running the latest version of the firmware and are protected with a strong password. They can also disable remote administration, change its default local IP address, and hardcode a trusted DNS server into the operating system network settings.
via: thehackernews




Leave a Reply