Bluebox Security some time ago discovered a vulnerability in nearly every Android device released in the last four years that allowed attackers to modify code of legitimate applications without breaking their cryptographic signature. Hackers can exploit the vulnerability for all kinds of malicious activities, including data theft or abusing infected devices as botnets.
You can read up on the technical details of the vulnerability on the Bluebox website. Google in the meantime has created a patch for the issue which it delivered to Android device manufacturers. It is however up to each individual manufacturer to deploy the patch, so that your device may have received it already, or is still vulnerable to the exploit.
Bluebox has released a new application for Android that checks whether your smartphone or tablet is vulnerable or patched. Simply go to Google Play and install the Bluebox Security Scanner application from there.
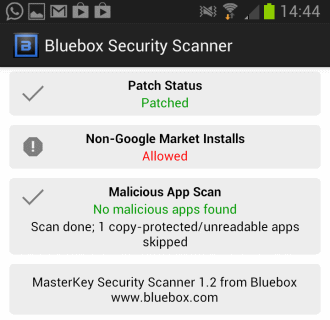
All you have to do then is to run the application on your phone or tablet to find out if it is patched or not:
- Patch Status indicates whether your device manufacturer has distributed the patch already or if your device is still unpatched and therefore vulnerable to the MasterKey exploit. The status reads unpatched/vulnerable in this case.
- Non-Google Market installs checks if application installations from unknown sources are allowed on the device or not.
- Malicious App Scan scans all installed apps for traces of malicious code and will report back to you if any are found so that you can react immediately to the threat.
The scanner cannot scan apps in the copy protected folder under /mnt/asec/ due to operating system limitations.
You do not need to do anything if your device is listed as patched. If it is unpatched, you cannot really do a lot about it either. What you should do however is be very careful in regards to new application installations, especially if they come from sources outside the Google Marketplace.
From the looks of it, it appears that Samsung has already pushed out the update to its devices, and that HTC has already patched at least some of the company’s devices as well.
Verdict
The application highlights if your system has been patched or not which may ease your mind if it is already patched or at least make you aware of the issue if it has not been patched yet. You can uninstall the application if the vulnerability has been fixed on your device, but may cling on to it if it has not. (via Caschy)
Via: ghacks




Leave a Reply