For many, the holiday season is a season for shopping and spending. But cybercriminals see it in a different light—they see it as a prime opportunity to steal.
Take, for example, online shopping. Malicious websites to try and trick online shoppers into giving them their money instead of the legitimate shopping websites. These sites are often made to look exactly like the website they’re mimicking, and feature a login screen that asks the user to enter their personal information. They are interested in any and all kinds of login information – for example, we recently saw phishing sites that stole the Apple IDs of users.
Trendmicro has kept track of the number phishing sites created since 2008. We pay particular attention to those that target Christmas shoppers and/or have holiday themes. There are plenty of these, and they persist all year. Unsurprisingly, they rise towards the end of the year, as seen in the graph below:
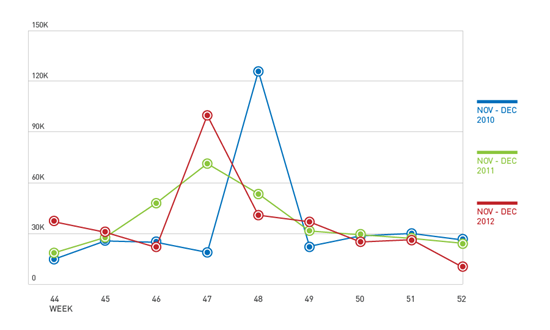
Figure 1. Christmas-related / Holiday-themed Phishing Sites
These sites also peak during big shopping dates, such as Black Friday and Cyber Monday. Online shoppers tend to search for huge discounts on these dates.
Cybercriminals target specific items that users might be looking for in particular when shopping online, such as gadgets (tablets, smartphones and DSLR cameras) toys, video games/consoles, software, and so on. We examined the most popular items sold and wished for on online shopping sites and compared them with the phishing sites we saw. We found that these were the most targeted items:
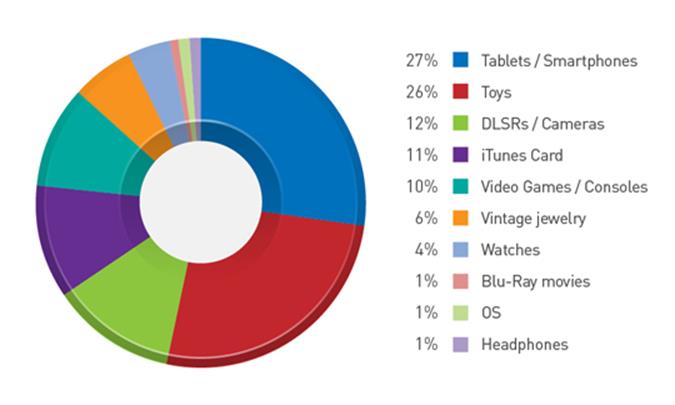
Figure 2. Top 10 Most Targeted Shopping Items
Spam campaigns also take advantage of the season. Recently it was found that a spam campaign which targeted British users. This campaign promoted cheap flights to destinations in the Canary Islands—popular tourist destinations for Britons. The name of a well-known provider of travel packages was also used.
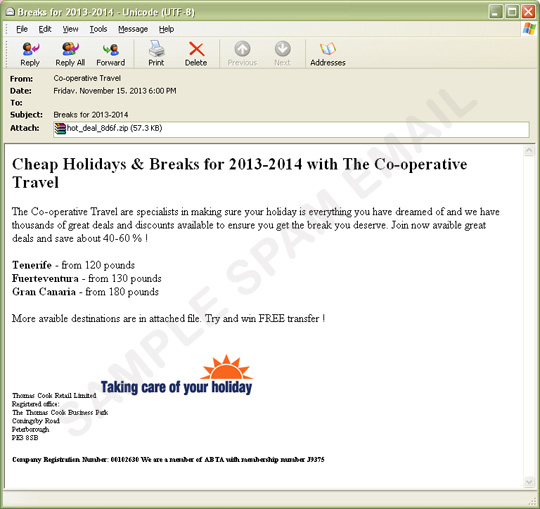
Figure 3. Sample Holiday Spam
The email contains a .ZIP file that claims to contain more available holiday destinations. Opening the archive yields a .PDF file that is actually a malicious executable file. (trendmicro detect this file as TROJ_DLOAD.NOM.) Its final payload is a ZBOT variant, which can steal critical personal information of users from their systems.
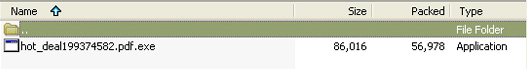
Figure 4. Malicious File In Archive
Users can avoid these threats by following these tips:
- Don’t use search engines to find good deals. Web threats lurk in search engine results, and they’re often pushed up to the top of the first page because of Blackhat SEO. Instead, bookmark popular and well-established shopping websites and do your searching from there.
- If it’s a deal too good to be true, it probably is. Half-off promos and amazing discounts certainly exist (more so during the holidays) but if it’s from an unfamiliar website or simply just beyond any reasonable sense of scale, then chances are it’ll lead to a web threat.
- Use online shopping apps instead of using your mobile browser. If you’re a huge online shopper and you use your mobile device to do all your buying, check if your favorite site has an app and use that instead. This allows for a more secure transaction between you, the customer, and the website itself—removing the chance for web threats.
- Install a security solution. A security solution can easily remove the risk of you accidentally stumbling onto opportunistic web threats when you’re shopping online by blocking malicious websites before you can even get to them. It also detects and removes any suspicious files or malware that may end up in your devices.
Via: trendmicro




Leave a Reply