Users of a fitness tracking app have inadvertently exposed the locations of military bases by publicly sharing their jogging/cycling routes.
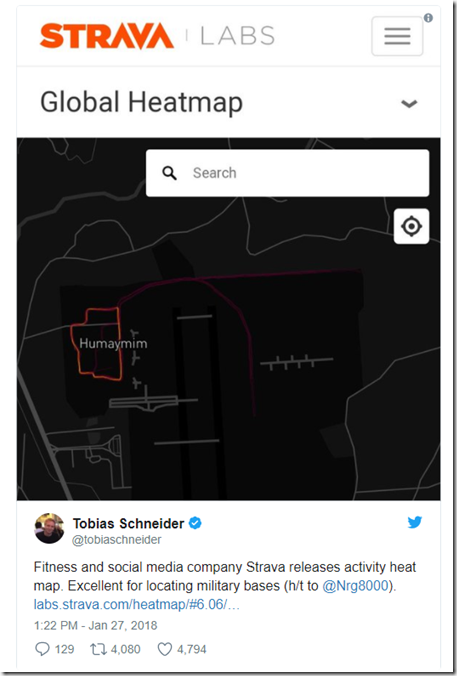
Many service people who use Strava, an app which allows them to record their exercise activity using GPS plotting, are sharing their data publicly. Their movements have ended up in Strava Labs’ Global Heatmap consisting of three trillion latitude and longitude points. That resource provides crucial information about how service people move and, by extension, yields insight into where they are stationed.
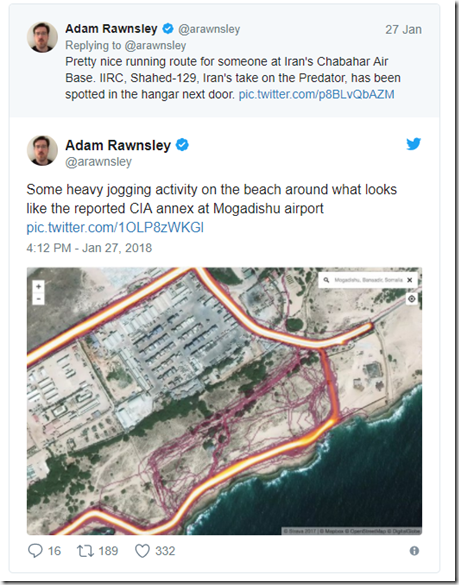
For instance, Adam Rawnsley of The Daily Beast used the information to hone in on the location of a possible installation for the U.S. Central Intelligence Agency:
Others have leveraged the Heatmap to identify patrol routes and bases:
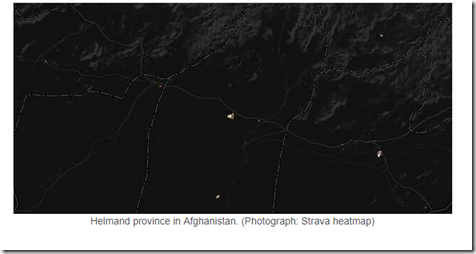
Nathan Rouser, a student of international security, first came across on the map on a mapping blog and decided to look deeper, The Washington Post reports. Such curiosity led to his discovery of what appeared to be U.S. soldiers’ activity in Syria. He began tweeting about his findings on Twitter, which led other users of the social media platform to do their own digging. Those investigations have uncovered the locations of potential Patriot missile sites and supply routes connecting bases in Afghanistan.
In response to Rouser and others’ revelations, the Central Command for the U.S.-led coalition against the Islamic State said it is in the process of revising its guidelines for service people’s use of wireless devices in and around military bases. As quoted by The Washington Post:
The rapid development of new and innovative information technologies enhances the quality of our lives but also poses potential challenges to operational security and force protection. The Coalition is in the process of implementing refined guidance on privacy settings for wireless technologies and applications, and such technologies are forbidden at certain Coalition sites and during certain activities.
Strava has in the meantime said it is “committed to working with military and government officials to address sensitive areas that might appear.” It’s also urging some users like service people to adjust their app settings to private, which will effectively limit their data-sharing to just the app itself.
News of this discovery comes more than three years after ISIS supporters hacked the U.S. Central Command’s Twitter account.
via: tripwire




Leave a Reply