Researchers have spotted a malvertising campaign that is believed to have affected at least 288 websites.
On April 10th, the Security Operations Center (SOC) at Fox-IT, a cyber threat management company, first detected the campaign after observing a spike in the number of incidents related to exploit kits.
“The incidents originated from a large malvertising campaign hitting the Netherlands,” explains the security firm in a blog post. “The list of affected websites spreads across most of the popular Dutch websites. In total we’ve now seen at least 288 websites being affected.”
Some of the websites affected by this campaign include Nu.nl, the most-visited Dutch-language news portal at over 50 million views in March alone; Marktplaats.nl, a service that is similar to eBay; and other news and culture sites.
As explained by Sophos, malvertising is another name for malicious online advertising. Attackers create a malicious ad and push it out through an advertisement platform that might be used on trustworthy websites. The ad will attempt to download malware or other unwanted content onto a visitor’s computer.
That means the affected advertisement platform–not the websites–are responsible for pushing out malicious advertising content.
In this campaign, external scripts are loaded from the malicious ad. Those scripts redirect visitors to the Angler exploit kit, which has dropped Cryptowall 4.0 and other malicious software in other attacks.
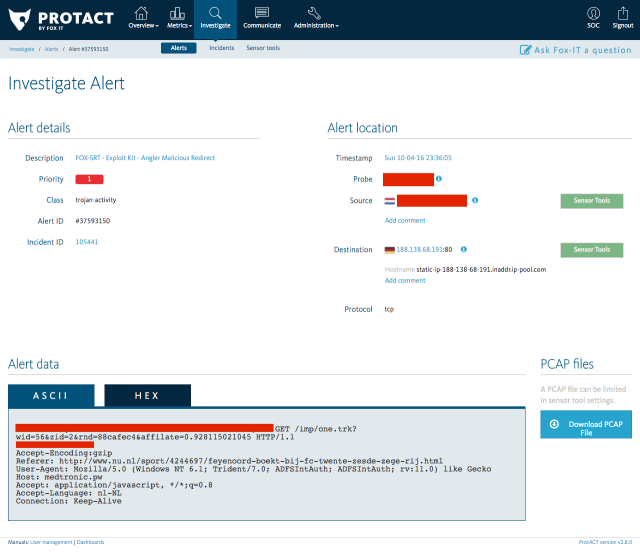
One of the redirects towards the Angler exploit kit, as observed by Fox-IT’s monitoring platform.
Two domains in particular, traffic-systems.biz (188.138.69.136) and medtronic.pw (188.138.68.191), have been observed to redirect users to the Angler exploit kit in this instance of malvertising.
After detecting the spike in exploit kit activity, Fox-IT contacted the affected advertisement platform, which has since responded to the incident and begun filtering the listed indicators of compromise (IoCs).
However, there’s still work to be done.
“They [the advertisement provider] will be tracking down the affected content provider as this issue has not been fully resolved, it has simply been filtered for now,” Fox-IT observes.
For more information on this malvertising campaign, please see Fox-IT’s post here.
Via: tripwire




Leave a Reply