During the last months the talk mainly has been about police virus infections, and more recently about CryptoLocker, the new major ransomware family.
However that doesn’t mean that our good “old friends” known as FakeAV aren’t around. Fake antiviruses have been infecting users for years and they have not disappeared, although it is true they are not as prevalent as they were in the past. This week we have seen a rise in FakeAV attacks using a new aggressive ransom-like approach.
The malicious file uses the following icon:
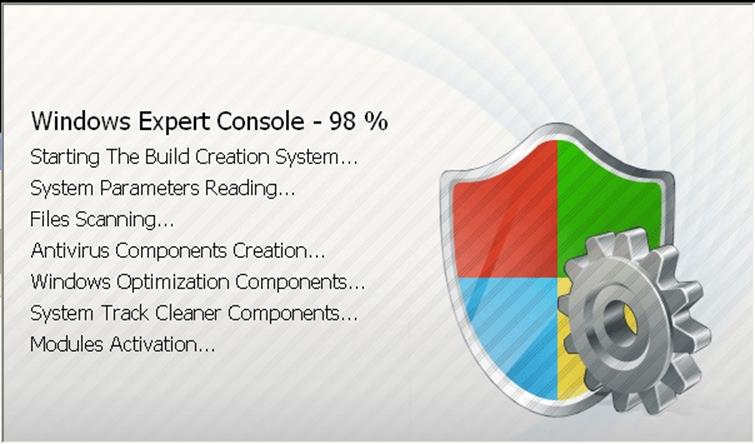
Usually it gets in the computer under the name “cleaner.exe”, although we have seen it using different names. As soon as it is executed, it appears a screen where it shows the installation of a program called “Windows Expert Console”:
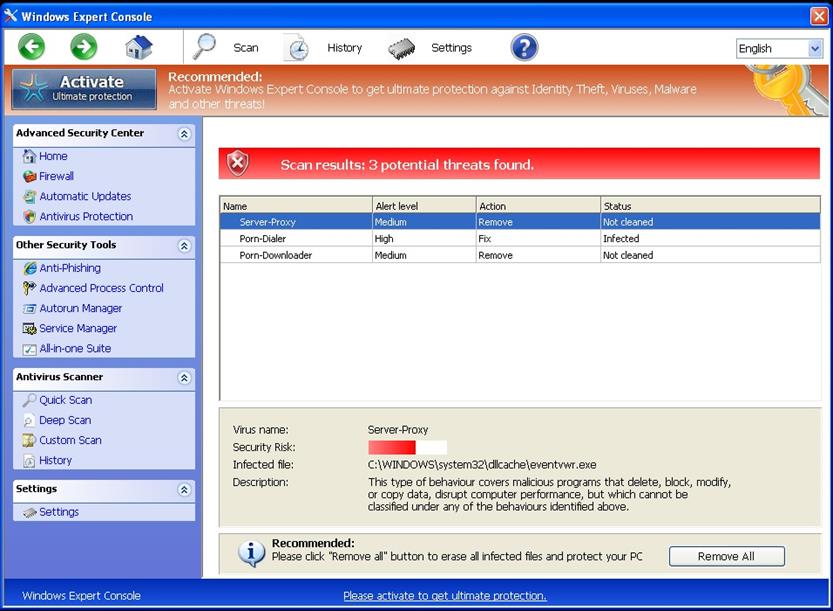
It only takes a few seconds, and before user is able to react it restarts the computer. Once restarted the following screen will show up and we won’t be able to do anything:
If you try to get back to the desktop or run any application, you won’t be allowed. The only thing you can do is to click on that “Remove All” button, and that will take you to a different window in order to buy a license of this FakeAV. It costs $99.
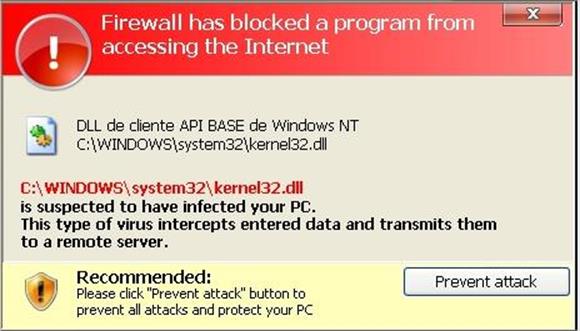
At the same time we found this malware, we detected another variant, this one is less aggressive (it does not block your computer) although they share the same interface, the only difference is the name, this new one is called VirusBuster, the same as the historical antivirus company that closed last year. In this case you get this kind of warnings to make the user pay the license fee:
As we mentioned, both programs share the same interface, and they are in 4 different languages (English, Spanish, German and French), in the following animated GIF you can see how they look like:
In case you have been infected with any of these, you can use one free malware removal tool Panda Cloud Cleaner.
Via: pandasecurity





Leave a Reply