Cyber attacks are all over the news, and it seems like no one is immune — Home Depot, Target, Adobe and eBay included. So why are CIOs still fighting cyber criminals with one hand tied behind their backs?
Shockingly, most companies are still relying on outdated, only partially effective methods to protect their sensitive data, mainly with technology that focuses on preventing incoming attacks. But actually stopping bad guys from slipping inside enterprise networks and getting their hands on sensitive data is nearly impossible these days. In fact, among organizations with over 5,000 computers, over 90 percent have an active breach of some sort at any given time. What’s worse, those organizations may not even know about it.
It’s time for CIOs to start focusing on the next line of defense in the war against cyber crime: an emerging area called breach detection, which focuses on identifying long-tail intrusions after they happen and mitigating their damage, partly through the use of big-data technologies. Your company’s information security may depend on it.
A Changing Battle Space: Prevention Is Not Enough
Surviving a shark attack is fairly simple: As long as you swim faster than the person next to you, chances are you’ll make it. Not so long ago, security was very much the same. As long as your company had better-than-average security, you were likely safe because someone else would get hit first.
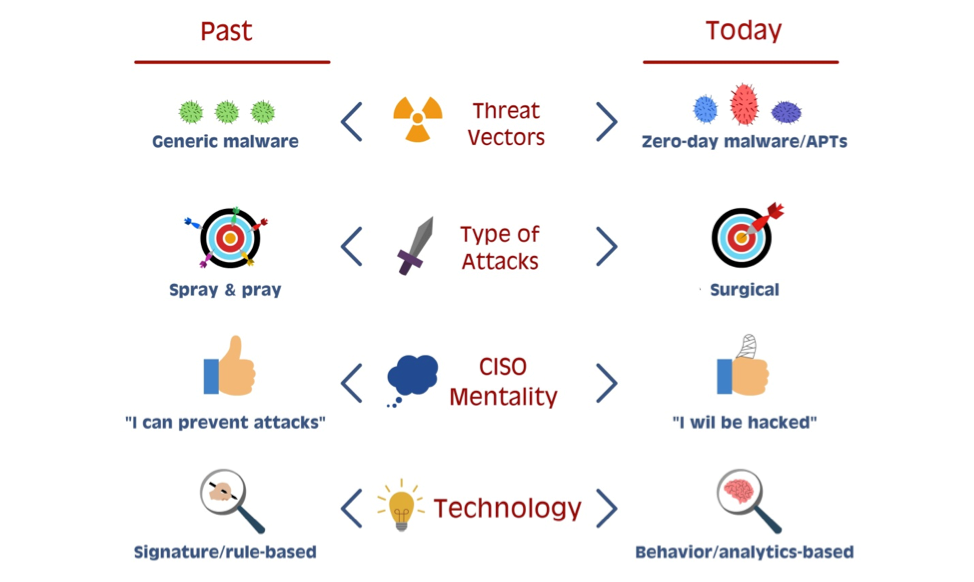
Hackers were looking for the “low hanging fruit” — the easy breaches. Online criminals mainly used a broad “spray and pray” approach to opportunistically find targets. In those days, “signature-based” security solutions, which tried to identify known, malicious code patterns and block them, made sense. If one company saw a new threat, a signature could be written for it and distributed to others to protect them from infection.
Fast forward to today. As organizations have bolstered their security, hackers also evolved. Attacks today are more sophisticated and targeted than ever before. Rather than sending generic malware, hackers today carefully plot each and every attack, using unique, “zero-day” exploits that render signature-based protections nearly useless.
While a number of new security companies, like FireEye, have surfaced in recent years to try to combat this type of attack, hackers continue finding creative ways around these tools. Some hackers go so far as to buy all of the same, state-of-the-art intrusion prevention systems their targets use so they can perfectly replicate the target’s exact security environment — then test their attack and virtually guarantee its success.
Most Damage Happens After Initial Breach
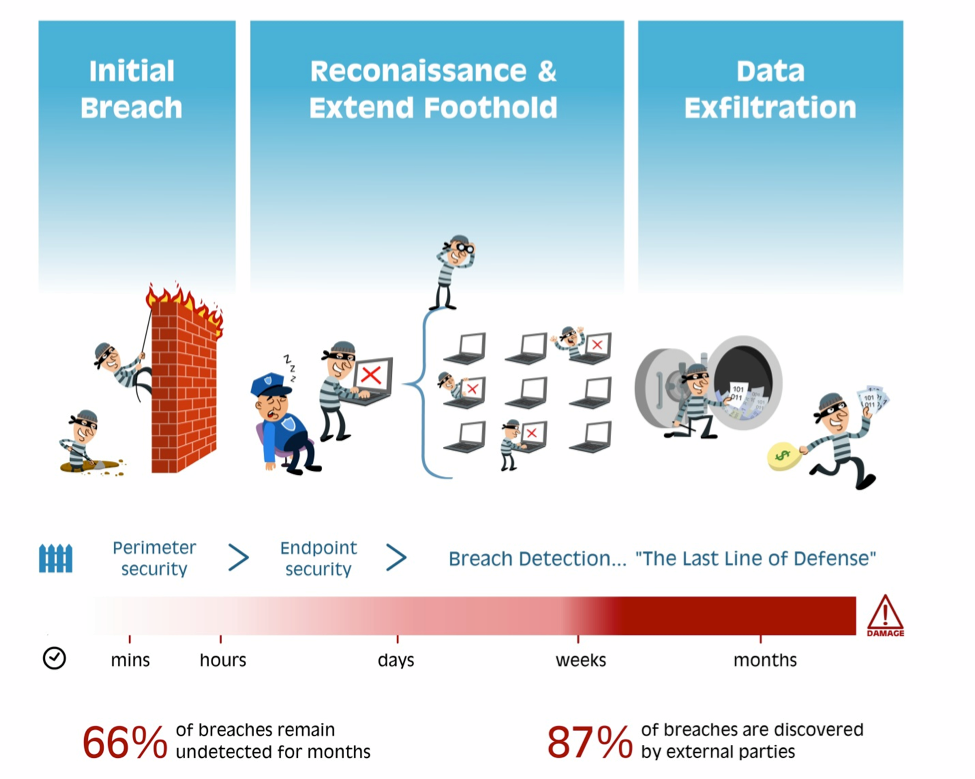
The initial intrusion in a typical breach scenario takes minutes to a few hours — in some rare cases, days. The real damage, however, occurs after hackers get around the first line of defense, making new, after-the-fact breach-detection efforts so critical. Once inside a target, it’s like discovering a gold mine. Hackers study their victim’s internal network, carefully extend their foothold and then begin mining the valuable data they find for months, if not years, before being detected — usually by accident.
Mandiant, for example, recently reported that APT1, one of China’s cyber-espionage units, attacked 141 victim companies across 20 industries and stole many terabytes of compressed data in sustained attacks averaging 365 days each. The longest attack lasted more than four years.
The most concerning part of all this is that very few organizations are now using new breach-detection technologies and can actually discover these ongoing breaches themselves, meaning attacks are even more destructive for their victims. Despite numerous alerts, Target, for example, didn’t detect the recent breach that led to 40 million stolen credit card numbers. Rather, it was only after the U.S. Department of Justice notified the company in mid-December that Target investigators went back to figure out what happened. According to a report published by Verizon last year, this is not uncommon — only about 13 percent of security breaches are discovered internally.
Breach Detection — The Last Line of Defense
All these factors point to the need for robust breach detection to provide a “last line of defense” against these attacks, instead of just focusing on blocking the initial wave of the intrusion.
While after-the-fact detection is not a new concept, the old generation of Intrusion Detection Systems (IDS) and Security Information and Event Management (SIEM) technologies generally fall short in today’s data-center environment. Why?
- They rely on pre-defined rules/signatures to detect breaches. In a world of bespoke attacks, such solutions will often miss the most relevant alerts.
- Low signal-to-noise. Imagine being flooded with hundreds or even thousands of alerts per day—each one representing a potential breach to your organization’s most sensitive data. It is no surprise that Target, like many others, missed the warning signs of the attack, like the proverbial forest for the trees.
- Limited visibility due to being deployed at the security perimeter or relying on log files. Without access to a rich data set that expands beyond the perimeter and includes all of the raw information (as opposed to a log file, which is a derivative of it), these tools are undermined in their ability to properly detect threats.
Next-gen breach detection is solving, in essence, a classic big-data problem: To be effective, these tools need to analyze a great variety of data in high volume, and at great velocity, to determine potential breaches. Most important, the tools must be precise; too many false positives and their reports will quickly be ignored, just like the boy who cried wolf.
A new crop of next-generation startups are working on this. They include Aorato, Bit9, Cybereason, Exabeam, Fortscale, LightCyber, Seculert, and Vectra Networks. Rather than relying on detecting known signatures, these companies marry big-data techniques, such as machine learning, with deep cyber security expertise to profile and understand user and machine behavior patterns, enabling them to detect this new breed of attacks. And to avoid flooding security professionals in a sea of useless alerts, these companies try to minimize the number of alerts and provide rich user interfaces that enable interactive exploration and investigation.
To help illustrate how these new technologies work, think of all of the online “breadcrumbs” that an attacker inevitably leaves behind during each step of the attack.
He generates network connections to command and control servers, for example. He moves across the organization in ways that are ever so slightly different from what’s normal; he may use whatever credentials he can get his hands on to try to access sensitive resources (e.g. tries to access proprietary code on development servers using a sales executive’s login). New breach-detection startups can sense all of these movements and changes. Combined with an intimate understanding of how hackers operate, they are able to finally piece together all the puzzle pieces in real-time before more significant damage has occurred.
There is a lot at stake here. In the end, solutions that effectively cut through the noise and point up just a handful of highly relevant, actionable security alerts will likely become an important “last line of defense” and a key component of the next-gen enterprise security stack.
Via: techcrunch




Leave a Reply